EDIT: OP has informed me it is not their personal IP. All is good in the land of Lemmy.
Must have quite a personal network for it to be a Class A address with 131072 subnets and 126 hosts. /s
Also, probably not a good idea to make memes with your real IP.
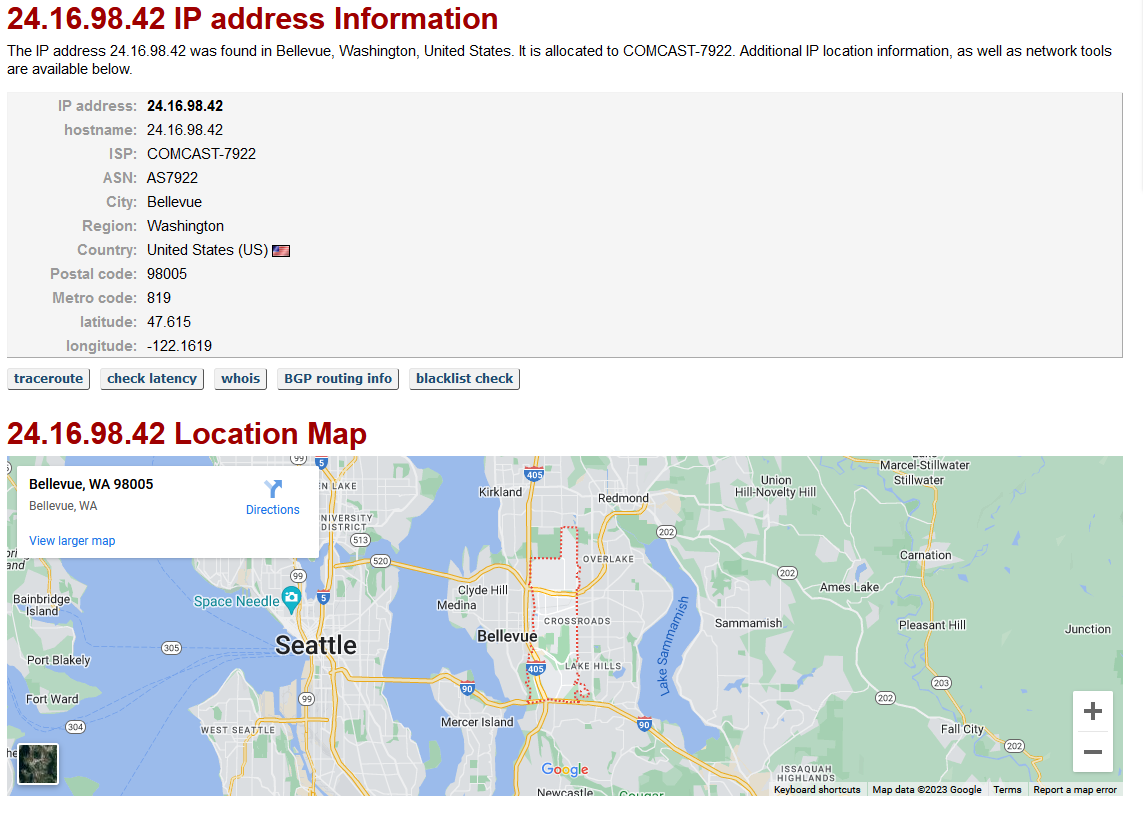
Not my IP; it’s just a random one that didn’t respond to pings.
Nice. Good old ICMP disabled.
Good for avoiding detection on a quick scan at least.
Give it that ol’ -Pn argument.
-sS80 -sA80 was my goto for CTF boxes.
Dont really see a problem with leaking ip adresses. You can get mine by doing a nslookup on my lemmy domain for example
It’s like putting your phone number on the wall of a bathroom stall. Maybe you won’t get a lot of prank calls, maybe you will. It’s a crapshoot.
The thing is, posting your public IP is like asking for a number of hackers to start probing your network for lapses in security. Not because you’re a juicy target, but simply because you put the information out there. That’s been bog standard for the internet for 20 years now.
Sure, IP addresses can be found through various ways, but having them out for everybody to see is just asking for more trouble than it is worth. You’re making yourself a target and creating more work for yourself if you’re constantly getting hacked because of it.
Like I don’t even want to do anything malicious and I immediately started up a traceroute.
A trip to shodan should be enough to convince you that ipv4 space is small enough that it really doesn’t buy you much to hide anything. Maybe a tiny bit of extra privacy by not associating an identity to an IP, but even that is pretty quickly blown away if you host anything identifiable. Which is the small web we’d benefit from restoring anyway.
The difference is a random IP is a random IP. You don’t know who it’s connected to. Once someone says “This is my IP” you now have it connected to a specific person, and other specific people may want to fuck with the original person.
Bots already scan all open IP addresses for vulnerabilities, but hackers live for people who give up information for free because fucking with someone who thinks they’re safe from it all is fun to them apparently.
Right, that’s the privacy aspect I mentioned. PII tied to your IP is now available, even if it’s just a pseudoidentity. But hosting anything also likely throws that out the window in the same way. Unless you have more users on your hosted service, but even then it narrows things down.
isnt that like… security through obscurity? not really a fan of that
So just put your phone number on the front page of Lemmy. Or are you practicing security through obscurity by not releasing it? /s
It’s not security through obscurity to not divulge information that need not be divulged. It’s not obscure if there’s lots of ways to find an IP. Like I said, it’s like putting a phone number out there. Like that one guy from 10 years ago who posted his phone number online and immediately regretted it because his phone just wouldn’t stop ringing. He wasn’t “afraid” until it totally fucked up his ability to use his phone. I’m just trying to be helpful. If you really want to put yourself on blast, go for it man.
deleted by creator
There are some things you can’t hide for the internet to work, such as IP addresses, so an IP address on it’s own is not privileged information. Announcing to the world that “this is my IP address” adds information and context which from a privacy perspective is privileged. If someone has an issue with you, they might target their focus to seeing if there’s a service running which is vulnerable at your IP, or they could initiate a DDoS against you.
If it’s your only layer of security, it’s not good. But when a website doesn’t tell you whether or not an email account exists when you try a username and password, it’s still obscurity (you’re not confirming one way or the other) but it’s still a useful level of security. IPs are generally not given out for a reason. Most people don’t even realize they don’t get hacked simply because they aren’t targeted. That you even route local traffic via the internet is interesting to begin with and makes me wonder if you truly are prepared for a targeted attack. Maybe you decided it’s not worth the effort but maybe you don’t know how. I don’t know. But nonetheless, you’re making yourself more of a target.
Of course that’s not OP’s IP address. It’s mine.
MFW my router doesn’t support hairpinning/NAT loopback
That’s it’s really annoying.
cries in shorewall
IPv6 might work
This is why I set up my pihole to send back the local server IP when I ask for my domain
Noob question. Would that request travel over the internet or is it resolved locally?
Depends. If the zone responsible for whatever resolves to that IP is hosted locally - then DNS request would stay local.
If the service behind that IP is running locally - then all traffic would stay local. Network stack would be smart enough to not run circles to find itself.
Yeah, the router ought to know that public IP belongs to a device in its own network unless you’re doing stuff like running your own router behind an ISP provided router and just forwarding ports instead of maintaining IP assignment / routing tables
Tell that to my opnsense box that refuses to NAT mirror.
If the router supports hairpinning, the IP request can be resolved locally.
The domain name lookup would be a different issue and could potentially need to be resolved externally, but the router’s DNS cache should be able to answer eventually.
That’s a WAN IP, so it would be resolved by external DNS then routed back
Why are you mentioning dns? This is an ip request, no need to contact a dns server
Because the title mentions having a domain, I guess.
Yes, that was the train of thought I was on. I equated “find” to “resolve” and I’ve been dutifully chastised.
Yeah no need for DNS but an ARP lookup would be in order.
Relateable

deleted by creator
Enable nat loopback on your router
May be called hairpinning depending on the device.
The client will look up your domain at whatever DNS it uses. It will return your public IP.
Client will send a packet with that as destination. It will reach the router which goes ‘I know! The call is coming from inside the house!’ and sends it to the server without modification.
The server gets it and sends a response, but the response is addressed back to client’s local IP.
Client gets the response, but that packet’s origin (in the header) is server’s local IP.
Client goes ‘wtf, I didn’t call you?!’ And drops the packet, still waiting for a response with your public IP as its origin.
This can be solved with the router modifying the appropriate traffic’s headers so that the headers match the expected, called NAT Loopback, or by using IPv6 global addresses.
It might also work running a local DNS server that returns your server’s local IP for a given domain, but that might yield certificate errors, and won’t work if devices ignore the DNS coming from DHCP.
I was using straight firewall rules for some years, but lost the template when the NAT Loopback checkbox started working (OpenWRT).
This is a great explanation, I wish I could’ve got you to explain a bunch of other network stuff to me back when I was learning
deleted by creator
Yeah, I just included the DNS part for completion’s sake 🙂
Hey same I don’t know why it doesn’t work. I need to use my server’s local IP when I connect from inside my house.
Couple good ideas already posted, but also you can update your hosts file with a ref to the internal IP, or if you are running your own DNS server, add an override for the domain
There’s a few devices out there that don’t offer NAT hairpin/loopback by default, such as Mikrotik.
deleted by creator
We have found the location of a Rebel base! It’s in Seattle, Washington.
First time I saw an internal IP that isn’t “192.168.x.x”
Im pretty sure it isnt internal.
It’s not internal, but there are other private address ranges beyond 192.168.0.0/16. 10.0.0.0/8 is another common one. Container platforms like to use 172.16.0.0/12.
Your router knows it’s in trouble when you call it by its government name instead of its 192.168.street.name
It’s a public IPv4 address in the picture.
There are 3 ranges of IPv4 addresses which are reserved for private use:
24-bit block 10.0.0.0 – 10.255.255.255 20-bit block 172.16.0.0 – 172.31.255.255 16-bit block 192.168.0.0 – 192.168.255.255
Oh wow… Didn’t know this lol. I thought that OP would be using their private IP to access their homserver from home. Turns out I got completely confused…
I think if they were using a private IP, there wouldn’t really be a joke. Of course the router can resolve an IP in its network. The joke is that they’re using their public IP from inside their network, and when the request gets the router, instead of resolving externally, it resolves to the public IP of the router itself.
I changed my local subnet to 10.1.2.0, because it’s much easier to type.
It’s not internal
that’s really not an internal ip
deleted by creator