- cross-posted to:
- privacy@lemmy.ml
- apple_enthusiast@lemmy.world
- cross-posted to:
- privacy@lemmy.ml
- apple_enthusiast@lemmy.world
cross-posted from: https://sopuli.xyz/post/12670977
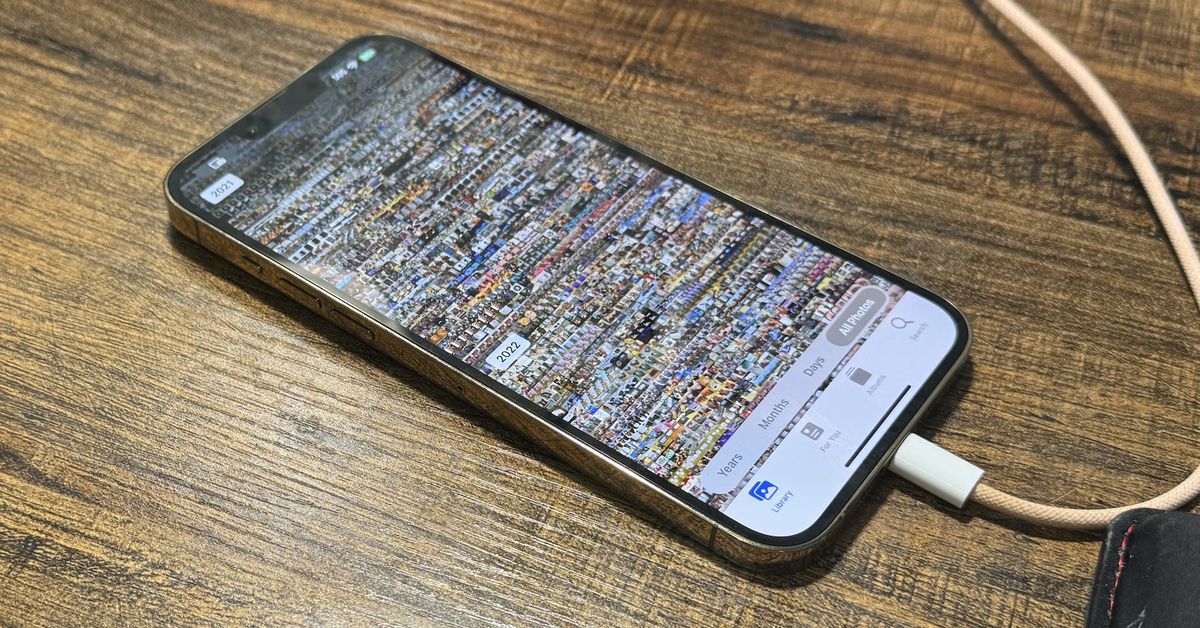
iPhone owners say the latest iOS update is resurfacing deleted nudes
I appreciate this thread’s nuanced discussion of how file deletion works from a technical standpoint depending on storage medium. But as a user, when I delete something, it should go away forever. I don’t care how.
I don’t care how
grabs your phone, throws it on the ground and blasts it with a shotgun
There you go! =)
Cloud’s deleted folder enters the chat.
Objective updated: shoot cloud server
Many years ago, we had a troubled employee leave work very mad. He was quite furious with his computer and went home for his revolver unbeknownst to us. He came back to work with it and unloaded all six rounds into the system. Each round went through the case and each one missed the drive/motherboard/videocard. So, the system was still working despite the abrupt extra cooling holes. This further incensed him and he went away even madder, but this time in cuffs.
Wow, how do you suck that bad at aiming?
It’s pretty easy if you don’t know where the computer’s vital organs are
You never shoot the
messengermonitor.
The computer is good at dodging without moving
It’s like how I can talk while holding my breath but only over a call
John Connor has entered the chat
I’ve been pleased with their messaging on that - “deleted items remaining trash for [some period]…“ (IIRC)
Well… if you really want to delete them…
takes blasted phone, insert remnants into small iron cup, places in inductive furnace
Hey at least I know it gets the job done
Hmm. I don’t know. Like, the actual surface involved in the storage is a lot smaller than the actual phone, and I imagine that you may-or-not destroy it with a given pellet.
I remember '80s movies – from a time when a lot of people weren’t all that personally-familiar with computers – where someone “destroying a computer” consisted of shooting its screen, which might be not that far off what would be happening. here. In fact, I bet that that probably has a TV Tropes entry.
googles
Well, they have a guy punching it, same kind of idea.
https://tvtropes.org/pmwiki/pmwiki.php/Main/ComputerEqualsMonitor
I will destroy this machine!
Yes! Now the other side will have to spend a whole $100 to replace it!
Might be kind of the same idea, just writ small.
I’ve started seeing people, who really should know better, referring to the PC tower as the CPU. As in, “I bought a bracket that mounts to my variable height desk which can hold my CPU up off the floor and let it move with my desk”.
Bro I’m looking at a picture of a custom water cooled PC here, you should know the fucking difference between a CPU and a computer case.
Eh, that’s been a thing for a long time. Decades at least.
I think that the problem is that there isn’t really a great term to clearly refer to the “non-monitor-and-peripherals” part of the “computer”. “Case” would refer to just the case, not what’s in it. “Tower” or “desktop” is overspecific, refers to particular form factors. I have a tower, but some people have under-monitor desktops (though that’s rare today) or various times of small form factor PCs. If I say “computer”, that doesn’t really clearly exclude peripherals.
And honestly, we don’t really use the term “GPU” quite correctly either. I’ll call a whole PCI video card a “GPU”, but I suppose that strictly-speaking, that should only be talking about a specific chip on the card.
8 bit games would label the computer player as CPU as a shorthand, I honestly probably got snapped at by a nerd sometime in my teens for making the mistake and got the central processing unit lecture so I don’t really make that association but I also never heard anyone pronounce “NES” not as an acronym prior to YouTube, so, I figure different people have different experiences also.
At one time I remember people commonly referring to the case as the hard drive.
I learned everything about how to build a PC from buildapc… like 12 years ago. Nowadays it has been infested by idiots who don’t know shit but act like they do, and also think more RGB = more better.
I don’t know what happened, but I put together a PC for the first time in some years, and holy mother of God, all the components have RGB LEDs slapped on them now. I had to actively work to find parts that didn’t have RGB LEDs on them (and I still accidentally wound up with some on the motherboard). I mean, yeah, LED case fans have been a thing for a while, and there was always a contingent that put electroluminescent strips on their computers. And it kinda grew into a lot of keyboards and mice. But now it’s a large portion of CPU fans, most cases, RAM sticks have RGB LEDs, motherboards have RGB LEDs. I didn’t have trouble finding non-RGB LED NVMe storage, or non-RGB LED SATA drives, but even there, you can get them. Hell, there are RGB LED cables.
I can only assume that a large portion of the people building PCs these days are doing it to have them physically blinged up.
Like, nothing wrong with wanting to do that, but I couldn’t believe the tiny proportion that wasn’t doing that.
I actually like having lights on the keyboard. Mostly because I can find rarely used keys in the dark.
The only way my box is blinged up is with tastefully beige-brown fans. I actually felt slightly betrayed by Noctua when they started making black fans.
You know what? They’re technically correct. There’s historically plenty of computer systems which came in multiple different cases, sometimes that’s still the case but the most obvious examples are historical, where you would get something like the CPU (yes) in one case and then a huge-ass card reader in another case and drum memory in yet another. Those drums were used as RAM. Each case was standing on the floor, at least chest-high.
Simply integrating various peripherals into the CPU doesn’t make the CPU any less of the CPU. Even ignoring the case thing and just looking at the CPU package (or even die): Modern CPUs contain a lot of things that would’ve been external to it, or even in a different case, in the past. You’ll hear the term “SoC”, system on a chip, thrown around but that’s misleading most CPUs nowadays are SoCs: You have your CPU cores, yes, but you also have a memory controller, you have storage interfaces and general IO (PCIe is a storage interface), as well as a GPU. It’s been a long time since mainboards came with northbridges. Newer CPUs may have enough memory on package to reasonably run without external memory (and not just “use the cache as ram during early boot” kind of stuff).
Easy peasy
Lemon squeezey
But as a user, when I delete something, it should go away forever.
Years of working tech support in my past tells me that this is a lie. “OMG restore this!”
I think tech would be a better place if it did actually go away when you deleted things. If something’s not explicitly backed up people really should have no hope of bringing it back.
If every time an OS had to delete something it had to fill the space with zeros or garbage data multiple times just to make extra sure it’s gone, we’d all be trashing our flash chips very fast, and performance would be heavily degraded. There really isn’t a way around this.
The solution to keep private files private is to put them into an encrypted container of some sort where you control the keys.
Step away from hardware constraints for a moment, and consider the OS:
If the OS says a file is deleted, under no circumstances should the OS be able to recover it. Sure, certain tools may exist to pull it back; but it should be unavailable to the OS after that. And yet, apparently a software update was enough to recover these files. Thus, the concerns about data safety in an environment where the OS cannot be trusted to remove data when it says it has been removed.
So let’s stop calling it “deleted” then, and call it what it is. “Forgetting”.
I’m not sure what you actually want the OS to do about it other than as I said, fill it with random data.
I think this is just semantics at this point, but to me there is a difference between “deleted” and “erased”. I see deleted as the typical “moved to trash” or
rmaction, with erased being overwritten bits, or like microwaving a drive.Edit - If i remember correctly deleting something in most OS’s/File Systems just deletes the pointer to that file on disk. The data just hangs out until new data is written to that sector. The solution, other than the one you mentioned about encrypting stored data and destroying the key when you want the data “deleted”, would be to only ever store data in volatile memory. That would make for a horrendous user experience though.
You can delete files by overwriting the data. On Linux its shred -zu [file]. Its slow but good to do if you are deleting sensitive data.
Its good its not the standard delete function.
Question: what fraction of bits do you need to randomly flip to ensure the data is unrecoverable?
Information theory aside: In practice all because you can’t write bit-by-bit and if you leave full bytes untouched there still might be enough information for an attacker to get information, especially if it’s of the “did this computer once store this file” kind of information, not the actual file contents.
If I’m not completely mistaken overwriting the file once will be enough to prevent recovering with logical means, that is, reading the bits the way the manufacturer intended you to, physical forensics can go further by being able to discern “this bit, before it got overwritten, was a 1 or 0” by looking very closely at the physical medium, details on how much flipping you need to defeat that will depend on the physical details.
And I wouldn’t be too terribly sure about that electro magnet you built into your case to erase your HDD with a panic button: It’s in a fixed place, will have a fixed magnetic field, it’s going to scramble everything sure but the way it scrambles is highly uniform so the bits can probably be recovered. If you want to be really sure buy a crucible and melt the thing.
Also, may I interest you in this stylish tin-foil hat, special offer.
If you delete normally, only the index of the files are removed, so the data can be recovered by a recovery program reading the “empty” space on the disk and looking for readable data.
If you do a single pass erase, the bits will overwritten one time. About half the bits will be unchanged, but that makes little difference. Any recovery software trying to read it will read the newly written bits instead of the old ones and will not be able to recover anything.
However, forensic investigation can probably recover data after a single pass erase. The shred command defaults to 3 passes, but you can do many more if you need to be even more sure.
Unless you have data that someone would spend large sums on forensics to recover, 1 to 3 passes is probably enough.
If it’s completely random then 50%, that’s how stream ciphers works.
Well, iOS could just do it like every other OS that don’t restore deleted data by installing an update.
Well, the storage device should handle that then. And modern NVMEs do. Self-encrypted drives are used to hide deleted information from an attacker that desolders the storage chips.
Edit: there are NVMEs that dont use self encryption, BUT they should still recognize a deleted sector.
That would apply in my “encrypted container of some sort” solution, yes.
Deletion commands are unfortunately not very reliable on many SSDs
It’s to prevent you from accidentally deleting a photo you would never want to delete. If you want to make sure it’s deleted, you just go into the Photos app and delete it from the Recently Deleted folder. I prefer this approach, as I have accidentally deleted a photo that I did not mean to, and luckily it was still there. Use cases are different though, so.
That still doesn’t fully erase the data though. It just tells the computer that that space on the drive is available to be overwritten, but the 1s and 0s are still recoverable
Right, right. I understand that. I was just explaining why the option is good for people like me. I don’t take nudes, and I don’t receive nudes, so I don’t mind if the data is still there or not. I’m just glad the photo of me and my friend was still there when I noticed it was missing from my album after a recent meme deletion spree. lol
The OS should never let that happen. It always should abstract the partition into a filesystem.
Imo there should be options for standard deletion and total deletion. Standard is faster, puts less wear on the drive, and keeps the files potentially recoverable, whole total would make it totally unrecoverable at the expense of taking slightly longer and putting a bit more wear on the drive
That is what thermite is for.
The second drive bay is the right size for a handy block of data erasing c4
No one will ever read my Zuck / Bezos fanfic.
Lol. I actually used to know a guy that claimed he used to have computer setup with a small thing to thermite on his hard drive and had set it up so if there were too many wrong passwords it would set the igniter off for the thermite. I don’t know if you really, did but he definitely had the technical skills to do that. He was one of those extreme early adopters of BSD and Linux who never used GUI. Oh and he was batshit crazy, legitimately I can see him thinking that was a good idea.
Nothing sinister, we just don’t delete what we say we delete. Instead we keep it in your profile to feed the algorithms and set the “deleted” flag to make you think it’s gone.
I mean, to be completely fair, that’s how data storage works.
We cannot really just make data disappear, so we let it get overwritten instead
But clearly the data is not overwritten and this was intentional. How do I know? Because that would amount to a massive amount of data, if it was de to a bug in Apple software or underlying filesystems, it would be detected in monitoring systems “Hey, we’re using 10x the data we should be, maybe we should look into it”.
The mistake was in the flag code that was supposed to fool us.
no when I say “overwritten” I mean that the area is set as deleted in the filesystem and the next time something writes to that area the data that was there before is disregarded.
and the next time something writes to that area the data that was there before is disregarded.
A single overwrite might not be enough to defeat physical forensics because shadows of the old data persist in how the new data is stored. Also when it comes to SSDs you might be waiting a long time for the data to get overwritten as the drive will wear-level its erm sectors (what are those things called with SSDs?).
They are called cells IIRC
So are you saying that they suffered from a filesystem bug that caused deletion failure? I’d imagine they use standard filesystems on their backend, I haven’t heard about any bugs like this.
If you ask me, what’s more likely, that a company known for shitty behavior lies about deleting files so they can continue to use that information to profit, – OR – that they are experiencing a filesystem bug on their backend, I’ll choose the former.
no I don’t believe a damn word of what apple’s gonna say on this, I just wanted to get the message out there that generally file deletion works by allowing data to be overwritten, so if the images are local this could very well just be that either it’s showing data that hasn’t been overwritten yet or it accidentally brought things out of the “recently deleted” depending on how long ago it was deleted.
Undeleting nudes

That’s iPhone
Seriously: I don’t think the cost benefit is there to intentionally make a maneuver like this. Any crap they pull needs to have a perfectly proper explanation, with our agreement to a specific term buried somewhere in their policies. Can only imagine how much money they blew throwing these billboards up all over the San Francisco Bay area. We have to buy Apple over Google for ostensible privacy gains, and Apple has to lock us in to their walled gardens to make up for their comparatively smaller ad/data business.
This post assumes Apple is aethical (that’s like amoral but for ethics right?) but still a self-interested economic actor. They can’t let short-term greed get in the way of long-term greed!
Seriously: I don’t think the cost benefit is there to intentionally make a maneuver like this.
You might be right
They can’t let short-term greed get in the way of long-term greed!
lol
deleted by creator
the shred command in Linux tries to do this, but it may not work if the hardware moves rewritten data blocks around to mitigate wear.
shreddoesn’t even necessarily work at the OS level. If you use something likeext3and I assumeext4, normally when you overwrite data in a file, you’re not overwriting data even at the logical level in the block device. Journalling entails that you commit data to somewhere else on the disk, then update the metadata atomically to reference the new data.It was more-practical in an era of older filesystems.
Proper deletion should include writing all ones or all zeroes to the block but y’all be lazy as fuck.
Only necessary on the ol spinning rust, with SSDs not only is it completely unnecessary, but it also burns extra writes.
Spinny’s store data magnetically on the platter with 1s and 0s, SSDs store data on the NAND as a held charge. If there’s a charge in the block it’s a 1 if there’s no charge it’s a 0.
With spinny’s, a file gets marked as “deleted” but the residual magnetic 1s and 0s will remain on the platter until eventually overwritten
With SSDs a file gets marked “deleted” and within no more than a few minutes TRIM comes along and ensures the charge on the NAND is released for that data, there’s no residuals to worry about like with spinny’s and is in fact necessary to ensure decent lifespans.
Wow, the SSD can hold the charges perfectly while unplugged for ages? Amazing.
In a post apocalyptic world where I am in charge of building a storage drive and I’m given all the instructions and fabs, the world is going without storage.
Wow, the SSD can hold the charges perfectly while unplugged for ages? Amazing.
Yup. Before flash memory, devices like video game cartridges which had game saves actually needed a battery to power the memory holding the saves.
I want a spinny as a pet now. Sounds cute.
But wouldn’t TRIM be the deleting he is requesting? Removing the charges would be setting all the bits in that block to the same value.
That just makes no sense to do, modern storage is write limited. As long as you used encryption the old bits mean nothing to anyone but you.
SSDs are. Big storage is not using SSDs.
I’m not an expert, but wouldn’t proper deletion be writing random ones and zeroes to the block? Multiple times?
I don’t think it’s been shown to make a difference.
It certainly feels more deleted…
It was sort of true in the past, but not anymore. I think writing random data once is probably fine, even for most state level actors.
yeah cuz for normal, day-to-day use that’s exponentially slower the more you’re deleting
You can do that when you wipe something.
Yeah, such as sensitive photos
Nitpick: it should be fuzzed with random 0s and 1s.
That’s skipping over the fact that recovering deleted data, even if it isn’t overwritten, is not an “oops”. It it takes extra effort, and if that data isn’t being protected it would be overwritten incidentally as drives are used.
There is a big difference in a database between “flagging” data and actually removing the association of the data to the database.
The data just needs to be overwritten to be truly deleted.
That’s how a lot of people handle deleted data in database, it’s literally just a flag. That’s why there’s a recommendation to edit Reddit posts before deleting them, to ensure they’re actually overwritten so they can’t just be restored.
deleted by creator
Yes, that’s certainly possible, but it’s also out of my control. I have basically three options:
- Delete account - we know this doesn’t delete comments
- Delete comment - “seems” to delete comments, but we’ve seen comments get restored - so probably using a “deleted” flag
- Edit comment with nonsense and when delete - should poison comment if they’re just using the deleted flag
That’s it. There’s no guarantee it works, but it has a much higher chance of working than the other two.
And there’s a good chance they delete old backups. Hosting every edit is expensive, so there’s a decent chance they clean up old data after some months.
deleted by creator
Funny how you think an edit doesn’t write the old record to a comments_old table
Well, there’s a non-zero chance they were too lazy to implement that.
They don’t care about your security or privacy, they care about being the exclusive vendor of your personal information.
If you never had any nudes in the first place, and update, is there a chance to get some?
Asking for a friend.
You should check out the federated backup of Apple Cloud. You can reach it at lemmynsfw.com. I mean your friend.
Every time I go looking, there’s a barren desert of male/gay content. In some lateral communities, furry porn is beating the content ratio like 10:1.
Y’all need to hold your phones or something while you browse the 5 billion straight communities, give me something that’s not weeks+ old. Uncut guys to the front of the queue, thanks. 📸
Be the change you want to see in the world
The only problem with that server is there are tons of shit you’d rather not see. It’s sadly not as easy to filter like the reddit porn subs are.
Is it that bad? I’ve been making a habit of blocking every community that shows up that I don’t want to see. So these days I rarely see stuff I really don’t want to see.
It just gets tiresome when you have to block 100 communities for the 15 you wanna see
In that case just subscribe to the 15 you want to see then?
Kinda hard to find them if you don’t know they exist in the first place.
I think that already happened and was called “The Fappening”. You can still find it with Google.
I remember the night when I found out about that and saw Jennifer Lawrence was one of the victims 😍

Good job Lemmy
Check your DMs 😏
Just the nudes. Nothing else.
deleted by creator
Not true, it specifically states in the article that, for example, one user had over 300 photos reappear, “some of which were revealing”. This is obviously not great but it isn’t likely as scandalous as it’s being made out to be.
The joke --------->
You ¯\_(ツ)_/¯
It was kinda wrote like a statement. People who didn’t read the article will read it as such, misinforming people
Have you always been a pedant or is this a recent development?
If misinformation is a minor issue to you, then I can’t do better
There’s so much misinformation online, sure it could have been a joke but it’s so easy to just be lazy, read the comment straight and move on acting like there’s some kind of operation going on at Apple stealing your nudes. I don’t really care if it’s a joke or not, and you’re not even the OP so who are you to say it’s for a fact a joke?
That was the case for me, until I decided to read the article
What article, it’s just a link. If I can’t read it here it ain’t there.
We shouldn’t encourage post-bot behaviour in the posters, title+summary or gtfo.
Since we’re being pedantic: the word you’re looking for is “written” not “wrote”.
I think you may have speeded to a conclusion.
I don’t see where I’ve mentioned a small English mistake. I said that it was written like a statement, which could misinform people
It’s scandalous regardless. The nudes just highlight the danger of this.
Cool
Next up, it starts showing other peoples nudes
There’s a post on reddit about some dude who gave his phone to a friend (wiped it, new iCloud, everything), and the undeleted photos are from when OP owned the phone.
With a factory reset the phones encryption keys will be destroyed and nothing should be retrievable from that device. Even if the data isn’t overwritten, without the encryption key no one could read it.
At least that’s my understanding of the modern safety- and encryption features of recent phone models/mobile OS’s.
The worst part: Apple’s iCloud is end-to-end encrypted and even Apple can’t see the users files, at least that is what they say.
If what the dude on Reddit states is true, then this is bad, really really bad! 😮
you can enable end to end encryption, it’s optional. I don’t think it’s enabled by default.
Not all of iCloud is end to end encrypted unless you manually activate their extra secure mode (which disables a few features too)
It does happen I have a buddy who sold his phone to another buddy they reset it but there was still random files and stuff on it even after factory reset
hey guy I’ve got a buddy too
Link pls?
“I know it’s not your nude, but it’s a nude and that’s what you were looking for, right?”
Of course it’s company policy to never imply ownership in the event of a nude. It’s always the indefinite article “a” nude. Never “your” nude.
That’s a feature, not a bug
I mean that’s what is happening if the phone used to belong to someone else
Computer data is never actually “deleted” until it’s overwritten with new 1s and 0s — operating systems simply cut off references to it.
That’s not entirely correct, and I would expect a tech news site to know but ig not.
It’s true with spinny’s since they store data magnetically on the platter with 1s and 0s, but SSDs store data on the NAND as a held charge. If there’s a charge in the block it’s a 1 if there’s no charge it’s a 0.
With spinny’s, when a file gets marked as “deleted” the residual magnetic 1s and 0s will remain on the platter until eventually overwritten like they say
But with SSDs, when a file gets marked “deleted” then within no more than a few minutes TRIM comes along and ensures the charge on the NAND is released (Which means that data is gone, permanently) for that data, there’s no residuals to worry about like with spinny’s and is in fact necessary to ensure decent lifespans.
This is dependent on the TRIM schedule. It could be size based (execute a TRIM when 50% of the blocks are used).
It could be or maybe the SSD has its own on-firmware TRIM schedule, but all major OS’s execute a TRIM on a time based schedule no longer than every 10-15 minutes.
Afaik the default for windows 10 is weekly via disk defragmenter, and that assumes it recognizes the drive as an ssd. I’ve had drives cloned to ssds that retain the hdd flag and had to setup a 3rd party tool that actually saw it properly and would trim as expected.
11 might have reigned that in… but probably not.
Perhaps, but this is unrelated. The magnetic charges may still be there, but if the reference to the content is deleted, how is the filesystem meant to know what file is there? This seems really suspicious to me.
TRIM works outside the filesystem, it does not care about 99.9% of it, the only part it cares about is if there is a reference in filesystem to the block charges. No reference == data to be released
There’s most certainly residuals, I’ve accidentally deleted then installed Windows on top of a bunch of my game saves. I found some random file recovery application and let it run for awhile. Guess what? Nearly everything was readable despite the fact it got wiped and then had a whole windows install.
NAND also experiences minor permanent damage on writes. Actually clearing the NAND involves a write as the charge has to be forced out (a write of 0s)
This can happen when TRIM is disabled
Here’s a study published last year I read that goes through this exact thing
In consideration of results obtained from the experiments, it concluded that the behavior of Wear Leveling in different SSD manufacturers having the same storage capacities does not match. It varies based on the number of files, types of files, and sizes. The recovery of files from different SSD manufacturers showed different results. In all SSDs, not a single trace of any file found in disk format scenario(s). Whereas, some of the data recovered in the delete case and from only one drive. It clearly showed different behavior of data recoveries in format and delete cases. The obvious finding from this study is that the time interval of image acquisitions played a significant role, and the longer time interval supports few chances of data recovery because the TRIM and Garbage Collection process effects clearing residual data from the drives
Edit: corrected links
Which means that data is gone, permanently) for that data, there’s no residuals to worry about like with spinny’s and is in fact necessary to ensure decent lifespans.
I doubt that the firmware is doing an overwrite of TRIMmed data. Rather, I expect it’s marking it as having been TRIMmed, and so can report that it’s zeroed to higher layers. If a higher layer queries the firmware for its content, sure, they might get zeroes returned. But if you can modify the firmware or otherwise bypass it, you may be able to get at the underlying media.
There is also the “bad block” issue, where storage media can take blocks – which may contain readable data – out of use, so that higher layers cannot access them. That applies to rotational drives and it looks like SSDs do the same thing. Again, might require bypassing or modifying the firmware to get direct access. But there can be data leaked there.
I also wouldn’t be terribly surprised if there is lingering information even after zeros are written to an SSD that might be recoverable if you could directly access the media, though I’m not familiar with the situation there. That is the case for rotational drives – the drive platter itself is “analog”, doesn’t just store a discrete string of ones and zeroes at the physical level. I once knew a cryptographer who was working on quantifying that leakage for rotational drives.
Now, attacking some of that is a pain and probably not a concern, but there are some cases where it might be a target. I once knew a professor who used to work at the Department of Defense, and he’d talk about their disposal process for rotational drives:
-
Drive has N random overwrites.
-
Drive gets passed through a rock-crusher device.
-
Remains get put in an acid bath.
I don’t know what they did if Step 1 couldn’t be completed due to drive failure. Maybe they were allowed to skip that step in that case.
That being said, probably most people don’t have to worry about the same level of resources being aimed at them.
EDIT: Step 1 might have been a degauss rather than an overwrite. Either way, it was definitely just aiming to twiddle bits, not physically destroy the drive. I’m trying to remember a conversation from a couple decades back…
I doubt that the firmware is doing an overwrite of TRIMmed data. Rather, I expect it’s marking it as having been TRIMmed, and so can report that it’s zeroed to higher layers. If a higher layer queries the firmware for its content, sure, they might get zeroes returned. But if you can modify the firmware or otherwise bypass it, you may be able to get at the underlying media.
TRIM is garbage collection and is a part of the wear leveling system. The whole point of TRIM is to have the SSD only hold the charge it needs too for still in use (i.e. not deleted) data. It’s the charge that damages blocks over time, so to extend lifespans it clears everything not needed. It’s not overwriting data for security or anything per se, but rather just a result of its longevity processes
Now, I’m sure there are cheap no name SSD controllers out there with ineffective TRIM operations that just lie about the operation, but any controller worth its salt is gonna have proper TRIM.
There is also the “bad block” issue, where storage media can take blocks – which may contain readable data – out of use, so that higher layers cannot access them. That applies to rotational drives and it looks like SSDs do the same thing. Again, might require bypassing or modifying the firmware to get direct access. But there can be data leaked there.
Part of that process is to move the data to another block and release the charge to prevent further damage, it’s possible the block is damaged in such a way that it won’t even release the charge, but if that’s the case it’s incredibly unlikely to be readable.
I also wouldn’t be terribly surprised if there is lingering information even after zeros are written to an SSD that might be recoverable if you could directly access the media, though I’m not familiar with the situation there. That is the case for rotational drives – the drive platter itself is “analog”, doesn’t just store a discrete string of ones and zeroes at the physical level. I once knew a cryptographer who was working on quantifying that leakage for rotational drives.
Yea it’s possible, but now you’re in the needing x-ray machines, powerful microscopes, full clean room labs and people with extensive, specific skill sets which means $$$$$$$$$$$$$$$$$$$$ or in other words, state level budgets range. 99.99999% of people will be fine
TRIM is garbage collection and is a part of the wear leveling system. The whole point of TRIM is to have the SSD only hold the charge it needs too for still in use (i.e. not deleted) data. It’s the charge that damages blocks over time,
I’m pretty sure that that is not correct.
The limiting factor is the number of writes. The reason that TRIM enhances life by facilitating wear leveling is that it lets the firmware know that the block no longer has useful data, so it can be returned to the pool used for wear-leveling. Without that, the firmware doesn’t know whether or not it can switch the physical block used to represent a given logical location and safely overwrite the existing contents of that new block.
The reason that TRIM enhances life by facilitating wear leveling is that it lets the firmware know that the block no longer has useful data
Ah I see the disconnect, TRIM doesn’t live in the OS outside of the firmware, TRIM is part of the controller firmware and is exposed as an ATA command for the OS to utilize
The study I have linked in my original comment goes more in-depth
Ah I see the disconnect, TRIM doesn’t live in the OS outside of the firmware, TRIM is part of the controller firmware and is exposed as an ATA command for the OS to utilize
Yes, I know.
The study I have linked in my original comment goes more in-depth
I’m on a phone, and it only partly showed up.
I mean, I read the PDF, the problem was the viewer bogging down.
googles
This sounds like what I expected:
https://superuser.com/questions/1060831/triming-as-alternative-to-securely-erasing-a-ssd
If data security is your concern, it should be noted that neither a SECURE_ERASE nor a TRIM actually erase the flash cells. The SSD firmware keeps a list of which cells are allocated and which are not. A TRIM simply marks a cell as unallocated the same way deleting a file causes the filesystem to mark a cluster as unallocated. No attempt is made to actually erase the data. A read request from an unallocated cell simply causes the device to return 0x00 (or some other bit pattern) without actually checking the cell’s contents.
There is no effective way of securely wiping an SSD. Forensics tools that can interface with the firmware directly can see the cells’ contents. Also, there is more storage on the device than what is accessible from user-space. These extra cells are used in garbage collection. Garbage collection can reallocate cells on-the-fly and can still work even on a drive that is 100% full. A SECURE_ERASE may (probably does) TRIM those cells, but a blkdiscard or fstrim certainly wouldn’t, since they use sector numbers to identify the areas to be TRIMmed.
The only way to securely erase an SSD is to destroy it. This is the policy of most companies in health care, banking, and government when surplussing equipment.
EDIT: I took a look at your PDF on a desktop. While it’s pretty light on the specifics of how they tested that the data was present, nothing there talks about anything below the OS level. My expectation is that what they did for their test was try to do reads from the device at the OS level and see whether it returned zeroes. They aren’t going to look below that. If they were interfacing with the drive at a firmware or below level, I’d expect them to have mentioned it, as it’d be a significant amount of additional work. And they don’t list relevant information like model number, much less firmware revision on the drive.
-
Surprise backup
Oh, it’s up!
Good thing I already knew Iphone wasn’t private.
I mean, they make you sign in with an Icloud ID
Never accepted the agreement, it constantly asks me to but works without it
Having said that, I am sure it still steals my photos because it’s close sourced
damn, user ilikeboobies, is security conscious? What a time to be alive.
Is it just nudes or is it all old photos?
The former would be hilarious, it would mean that iOS explicitly classified those images as nudes.
Indeed. But Apple does have the tech to analyze images/videos:
Apple’s CSAM detection capability is built solely to detect known CSAM images stored in iCloud Photos that have been identified by experts at NCMEC and other child safety groups.
which means they exported this task to some Indians overaeas… fuck which is just worse
ok so probably not, CSAM detection, specifically modern detection the kind that MS does, is based on image hashes, and how it works is that the law collects and creates the hash sets for these images, and distributes them to tech companies, who can then use them to calculate against hashes of existing photos, and if a match returns, ladies and gentleman, we got em.
It’s using hashes, no?
I dont trust that client side scanning or other system components arent going through these half deleted files
The article is being disingenuous about data not being deleted unless it’s overwritten with 1’s and 0’s. Technically that’s true, but:
Most data being deleted is equivalent to a piece of paper being placed in a trashcan, and it’s “permanently” deleted when that trash gets hauled away to a landfill (or supposedly recycling but that’s another topic). Technically it’s still forensically accessible, but it isn’t accessible by any normal means. That piece of paper may not have been incinerated, but for the majority of practical purposes, it’s gone.
Apple never hauled the trash away, even though they claimed they did. There should be no way for them to accidentally restore those photos, just like there’s no way for you to accidentally get a piece of paper back in your trash bin after it’s been sent to a landfill.
Focusing on the 1s and 0s skips past the fact they failed to complete the first, obvious, essential step. If they didn’t delete it the simple way, they would never have gotten to the 1s and 0s step. This isn’t just a simple oversight, and those pictures were still very easily accessible, just not to the people who should have been in control of them.
In your analogy, they never even put the photos in the trash can. They just put a postit on them saying “don’t show to user”. Then the updated software forgot about the postits (and started to post tits).
can’t wait for my personally hosted, and managed hardware server to start serving me shit i never put up in the first place.
Oh wait that won’t happen, because i host it, and it’s mine, and i own it.
Well, someone obviously didn’t read past the headline: its undeleting images locally that haven’t been overwritten
yeah and i can’t have that issue because i use a real filesystem that isn’t schizophrenic, because if it was you would get dataloss
Thank fuck for nerds writing open source software. Otherwise my life would be hell.
merges WordPress into the apt repository for grep
watches the world burn
:)
deleted by creator
I’m a paper user and I burn all my letters using a large amount of heat.
I’m a stone tablet user and I throw my tablets off Mt. Sinai.
Im an etch-a-shetch user, and a good shake is all it takes.
Etch-a-sketch is clearly the superior technology. Everyone should just keep their nudes in etch-a-sketch form.
Instructions unclear, aluminum powder stuck in my naughty bits.
It helps erase whatever you drew if you shake the etch-a-sketch too!
I’m a signal flare user and this metaphor is really falling down
I’m an android user and I shred my files using a app that uses an algorithm that overwritten that bytes of the file
I suspect that it doesn’t actually work. I mean, they can overwrite the logical positions in the file file if they want, but that doesn’t entail that it actually overwrites the underlying physical blocks, for a number of reasons, starting with some of the stuff at the drive level, but also because of higher-level issues. What filesystem does Android use?
googles
Looks like yaffs2, at least on this system.
https://stackoverflow.com/questions/2421826/what-is-androids-file-system
rootfs / rootfs ro 0 0 tmpfs /dev tmpfs rw,mode=755 0 0 devpts /dev/pts devpts rw,mode=600 0 0 proc /proc proc rw 0 0 sysfs /sys sysfs rw 0 0 tmpfs /sqlite_stmt_journals tmpfs rw,size=4096k 0 0 none /dev/cpuctl cgroup rw,cpu 0 0 /dev/block/mtdblock0 /system yaffs2 ro 0 0 /dev/block/mtdblock1 /data yaffs2 rw,nosuid,nodev 0 0 /dev/block/mtdblock2 /cache yaffs2 rw,nosuid,nodev 0 0 /dev/block//vold/179:0 /sdcard vfat rw,dirsync,nosuid,nodev,noexec,uid=1000,gid=1015,fmask=0702,dmask=0702,allow_utime=0020,codepage=cp437,iocharset=iso8859-1,shortname=mixed,utf8,errors=remount-ro 0 0https://en.wikipedia.org/wiki/YAFFS
YAFFS is a robust log-structured file system that holds data integrity as a high priority. A secondary YAFFS goal is high performance. YAFFS will typically outperform most alternatives.[3] It is also designed to be portable and has been used on Linux, WinCE, pSOS, RTEMS, eCos, ThreadX, and various special-purpose OSes. A variant ‘YAFFS/Direct’ is used in situations where there is no OS, embedded OSes or bootloaders: it has the same core filesystem but simpler interfacing to both the higher and lower level code and the NAND flash hardware.
Yeah, note the “log-structured” bit there.
https://en.wikipedia.org/wiki/Log-structured_file_system
A log-structured filesystem is a file system in which data and metadata are written sequentially to a circular buffer, called a log.
So, what happens is that when you write, it’s going to the log, and then there’s a metadata update once the write is complete saying “I wrote to the log”. The app probably isn’t writing to the previous location of the data on the disk, because writing to byte offset 32,000 the second time in a file will go to a different logical location on the storage device than the first time you wrote it, causing the thing to not actually be overwritten.
googles
https://arxiv.org/pdf/1106.0917
Secure Deletion on Log-structured File Systems
We address the problem of secure data deletion on log-structured file systems. We focus on the YAFFS file system, widely used on Android smartphones. We show that these systems provide no temporal guarantees on data deletion and that deleted data still persists for nearly 44 hours with average phone use and indefinitely if the phone is not used after the deletion. Furthermore, we show that file overwriting and encryption, methods commonly used for secure deletion on block-structured file systems, do not ensure data deletion in log-structured file systems.
I’d also note that this is a lead-up to proposed solutions, but that’s only handling things down to the level that the OS sees, not what the flash device sees; they don’t mention things like wear leveling, so they probably aren’t taking that into consideration.
EDIT: Oh, they do mention it, but just to say that some of their approach might work (like, what they mean is that if it writes enough data in the background, it might eventually overwrite whatever, even if the OS has no control as to what’s being written):
Wei et al. [16] have considered secure deletion on flash storage in the context of solid state drives (SDDs). An SSD makes use of a Flash Translation Layer (FTL). This layer allows a regular block-based file system (such as FAT) to be used on flash memory by handling the nuances of erase blocks opaquely through the FTL’s layer of indirection. This layer has the same effect as a log-structured file system, where the FTL writes new entries at empty locations, so old entries remain until the entire erase block can be reclaimed. They executed traditional block-based approaches to secure deletion and determined that they do not properly sanitize data on flash storage. They also showed alarmingly that some built-in sanitization methods do not function correctly either. They propose to address this concern by having flash hardware manufacturers make use of zero overwriting, and add it into the FTL hardware. They state that circumventing the problem of a lack of secure deletion requires changes in the FTL, but depending on how the FTL is implemented, our userlevel approaches may also succeed similarly without requiring hardware changes.
So if I am reading this right thermite is the safest way to permanently delete my data right?
Well, physical destruction. Thermite maybe isn’t the best route.
Really, it depends on your definition of best.
Nope regardless of the situation. Thermite is always the best solution
It will be effective as fuck though.
Hm… I curiously checked my phone, deleted images/videos are still deleted and haven’t resurfaced. Then again I don’t mix technology with nudity. /shrug
There are tons of reasons to take nude photos… you often have to send in nude photos for the beginning stages of surgery consultations.
And sexting is fun.
This comment comes across insanely judgemental of the individual, when the issue is that Apple deleting data and thus violating privacy.
It’s not just nudes, though. This could happen for any deleted picture. I’m not really expecting them to zero out the file system block or anything, but this implies they’re not even doing file system level deletion.
i’m almost certain this is more of a cloud bug than anything. Fucking up the incredibly basic process of “hey this shit isn’t real, don’t look here for anything” is hilarious.
There shouldnt be a fucking excuse. Did you accidentally roll back an fs journal? No, good, because that’s how you get dataloss
Yeah… I think I’d rather do that in person than to video record or take images of myself nude. Privacy and security is a pretty big deal to me. Hence, I don’t mix technology with nudity.
You’ve never been in a long distance relationship? And as I said, some people need to take nudes for medical reasons. It’s not a hypothetical situation, I know multiple people who have done this.
It’s fine that you have your own personal philosophy for taking nudes, but your post is coming off as judgemental of those who do.
It’s not the individual’s fault, it’s Apple’s fault for being unclear about what the delete feature is actually doing.
Hm… I never felt a need to expose myself (using tech) to another person to feel validated or to get their (or my) rocks off or for any other reason, honestly. I’m not trying be morally superior, I’m just saying I don’t expose myself with technology as a medium. In fact, I’ve never posted a photo of myself on any social media. I take privacy and security seriously.
Plus look at the consequences of exposing yourself to others through tech… blackmail, image-based abuse/exploitation, revenge p*rn etc…
My initial comment was simply stating that Apple’s latest update hasn’t undeleted any of my photos/videos in general but that then again I don’t have any nude images/videos on my iphone/iCloud storage if the claim is that nude images/videos exclusively are getting undeleted.
Ah okay. I didn’t interpret this as only nudes being undeleted, so I was reading your comment in that light. Understandable.
I just want to appreciate an argument where both user names check out, considering the stances taken by the “whore” and the “square” per the names.
🔥🔥 YES
You don’t mix technology and YOUR nudity 😉
haha…
I love mixing technology with nudity. But I have also avoided this problem because I don’t mix technology and Apple.
So you use a de-googled android?
I think mixing tech and nudity is awesome! I love getting dickpics!
Did you think some else’s nudes might have resurfaced there…?
No they’re just feeling morally superior for no good reason.
As a rule, files never get deleted… They get over written. So it depends on whether that process has happened to any loose images.
Are they not happy when they got back what they thought was lost? :-)